Born from Artificial Intelligence,
designed to evolve
Prootego is the Italian cybersecurity platform that unifies endpoint protection, network intrusion detection, and offensive security in one integrated solution. Detects advanced attacks, correlates events across your entire infrastructure, and lets you respond in real time — before damage is done.
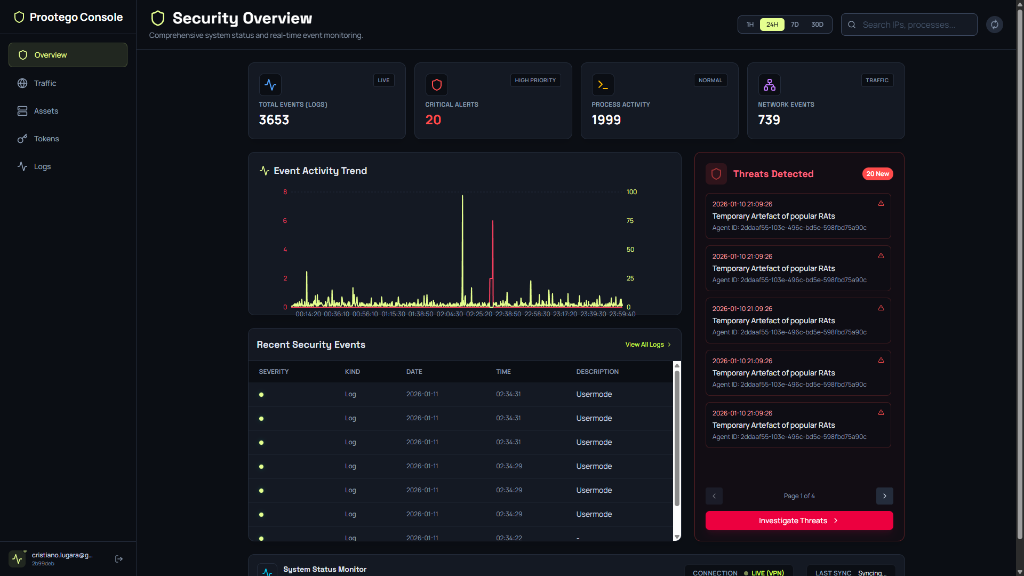

Security Overview
Real-time global threat map with connection tracking, agent monitoring, and alert aggregation.
Defense alone isn’t enough
Most companies focus exclusively on defense, without ever validating their security posture. Traditional antivirus and firewalls react only to known threats and offer no overall picture of an ongoing attack.
Passive Defense Only
Traditional solutions wait for attacks without proactively verifying infrastructure vulnerabilities.
No Network Visibility
Without traffic analysis, lateral movements and anomalies go unnoticed for weeks.
Fragmented Products
Endpoint, network, and offensive tools managed separately create blind spots between products.
No Offensive Testing
Without attack simulations, companies discover their weaknesses only when exploited by a real attacker.
Prootego changes the paradigm: defense, network analysis, and offensive security in one integrated platform. Proactive security — from prevention to attack simulation.
Complete Security Platform
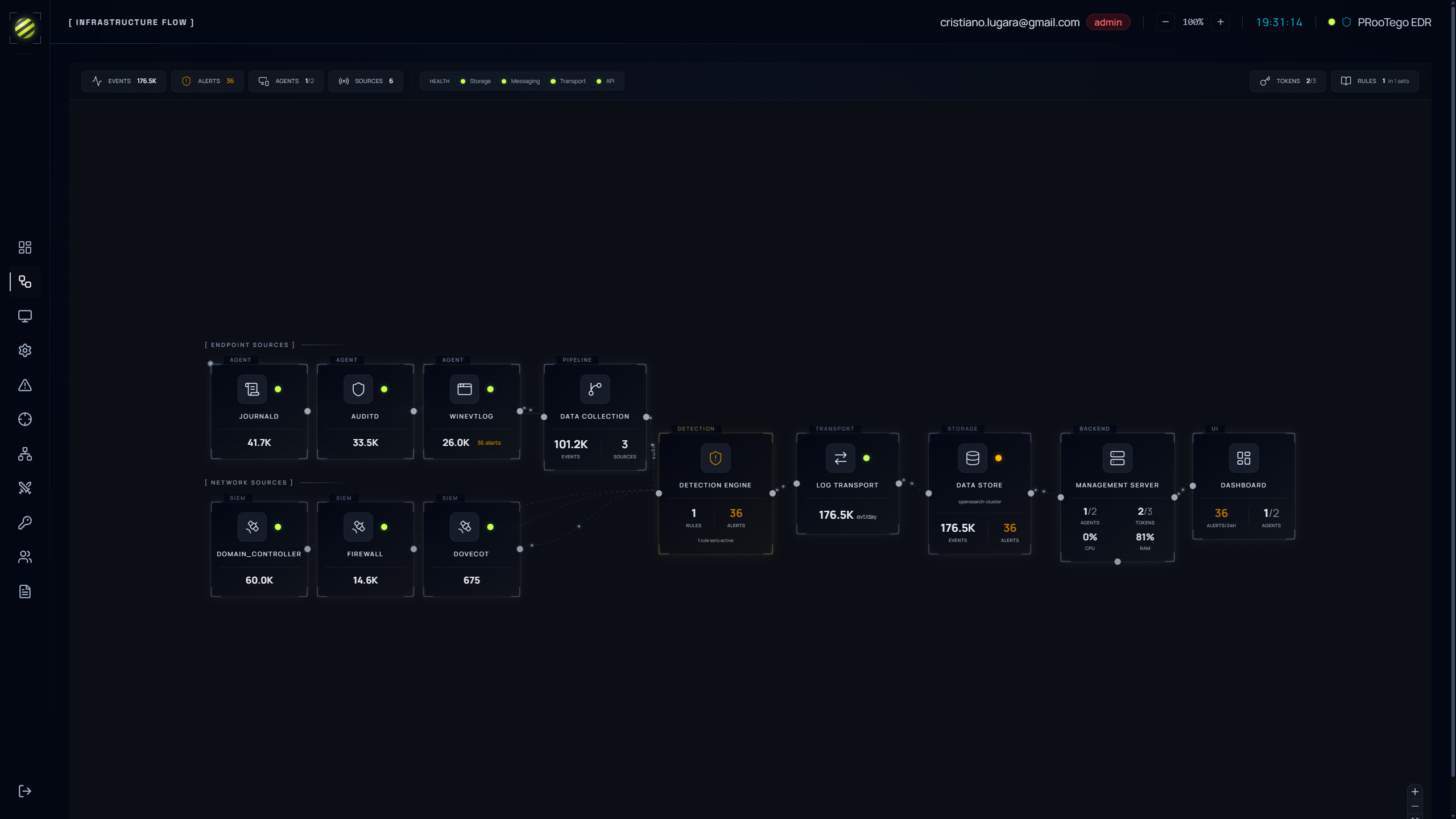
EDR, XDR, NIDS and SIEM unified in a single platform. Every feature built on open standards — Sigma, YARA, MITRE ATT&CK.
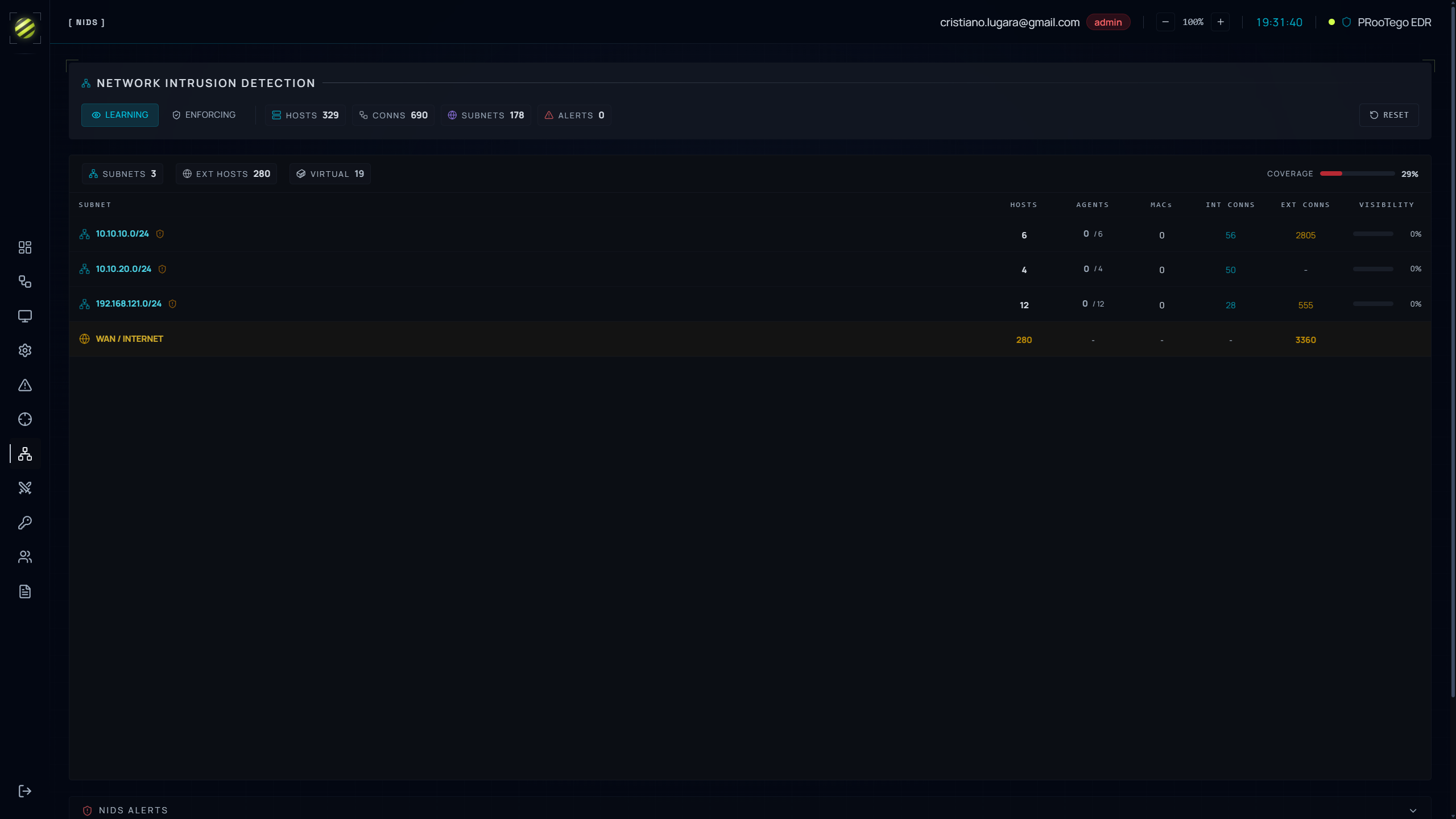
Network Intrusion Detection
Built-in NIDS that learns your network baseline and detects anomalies. Automatic subnet discovery, device tracking, GeoIP enrichment — switch between Learning and Enforcing modes. Any unauthorized device triggers an instant alert.
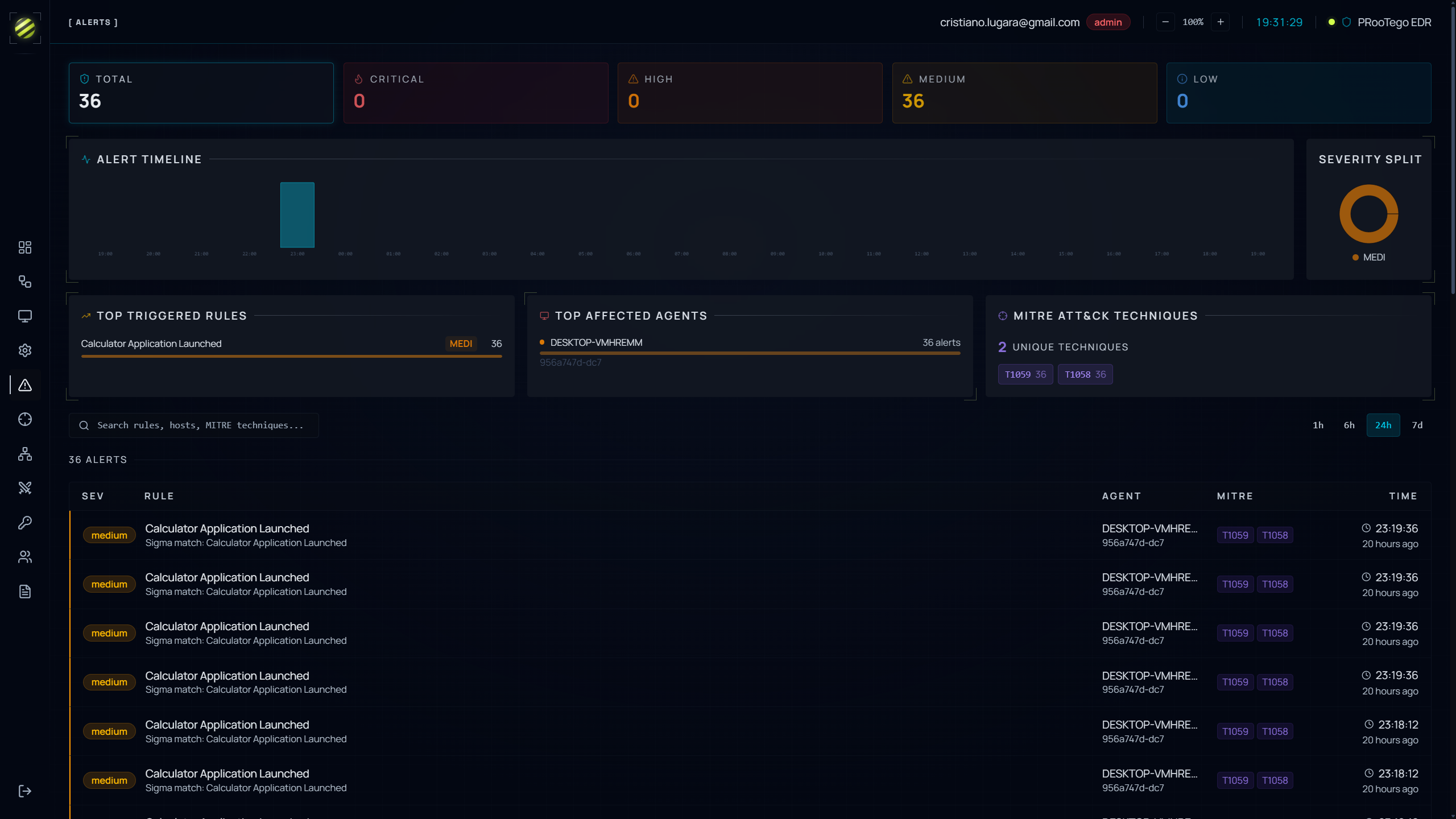
MITRE ATT&CK Coverage
Full MITRE ATT&CK matrix visualization showing your detection coverage across all techniques. Every alert is classified by tactic and technique — measure your security posture and identify gaps at a glance.
Docker Deployment in Under an Hour
Full stack deployed with Docker Compose — infrastructure up in under an hour with automated setup. Secure token-based agent enrollment. Onboard endpoints in minutes with no additional hardware needed.
Login Auditing & Compliance
Track every login across SSH, Windows, and Active Directory. SIEM log collection from firewalls and email servers. Immutable audit logs for GDPR, NIS2, and industry compliance — out of the box.
Real-time Telemetry
Live streaming of process execution, file modifications, network connections and system metrics. Native eBPF monitoring on Linux — kernel-level visibility with zero disk overhead and sub-second detection latency.
Remote Agent Control
Full remote control over every endpoint: isolate machines, block IPs, kill processes, quarantine files. YARA scans for malware patterns, forensic shell for live investigations, automated response via Sigma rules.
Multi-Layer Detection & Response
Sigma rules, attack chains, and multi-source correlation. Detects complex threats that evade traditional security tools.
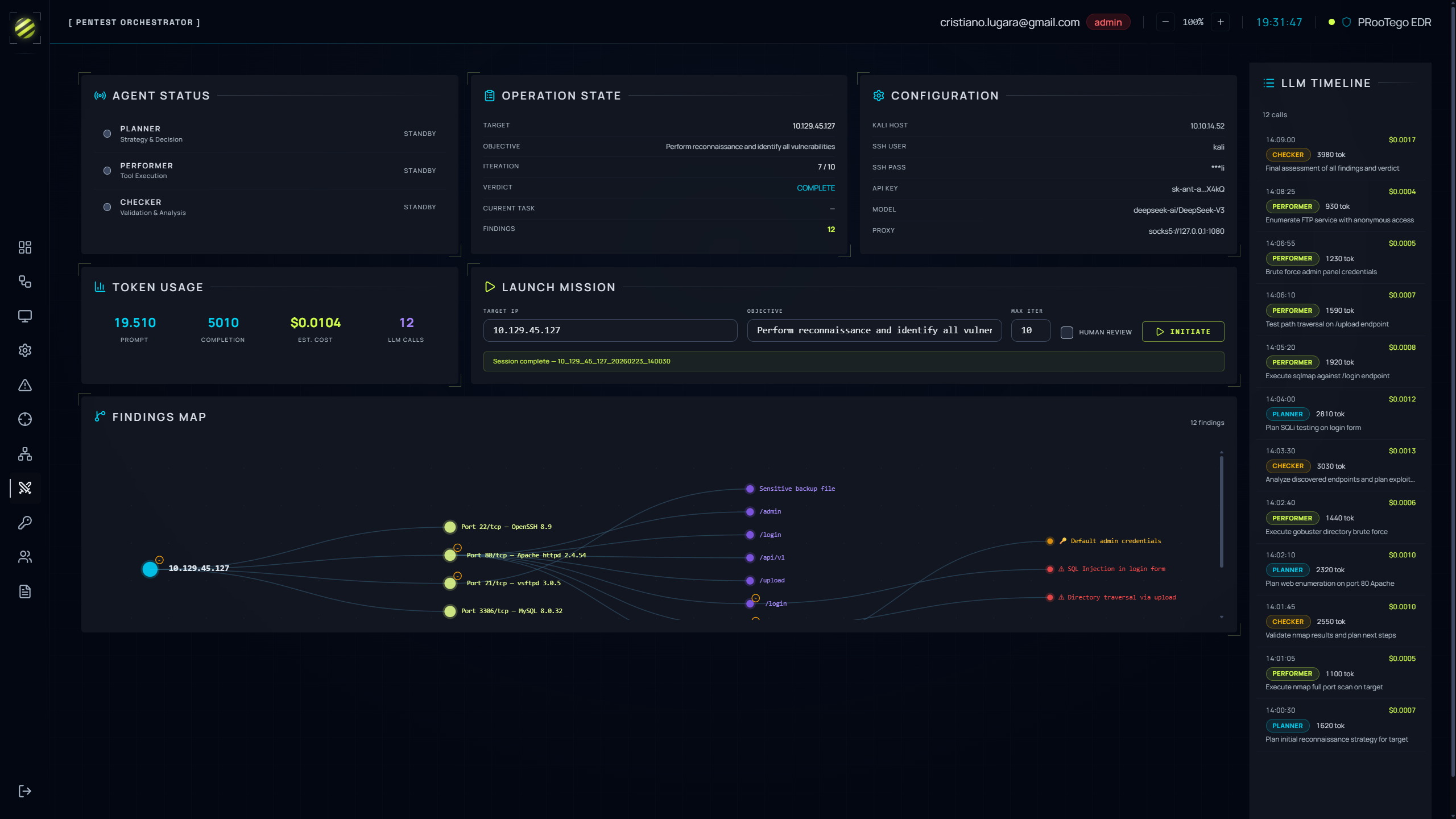
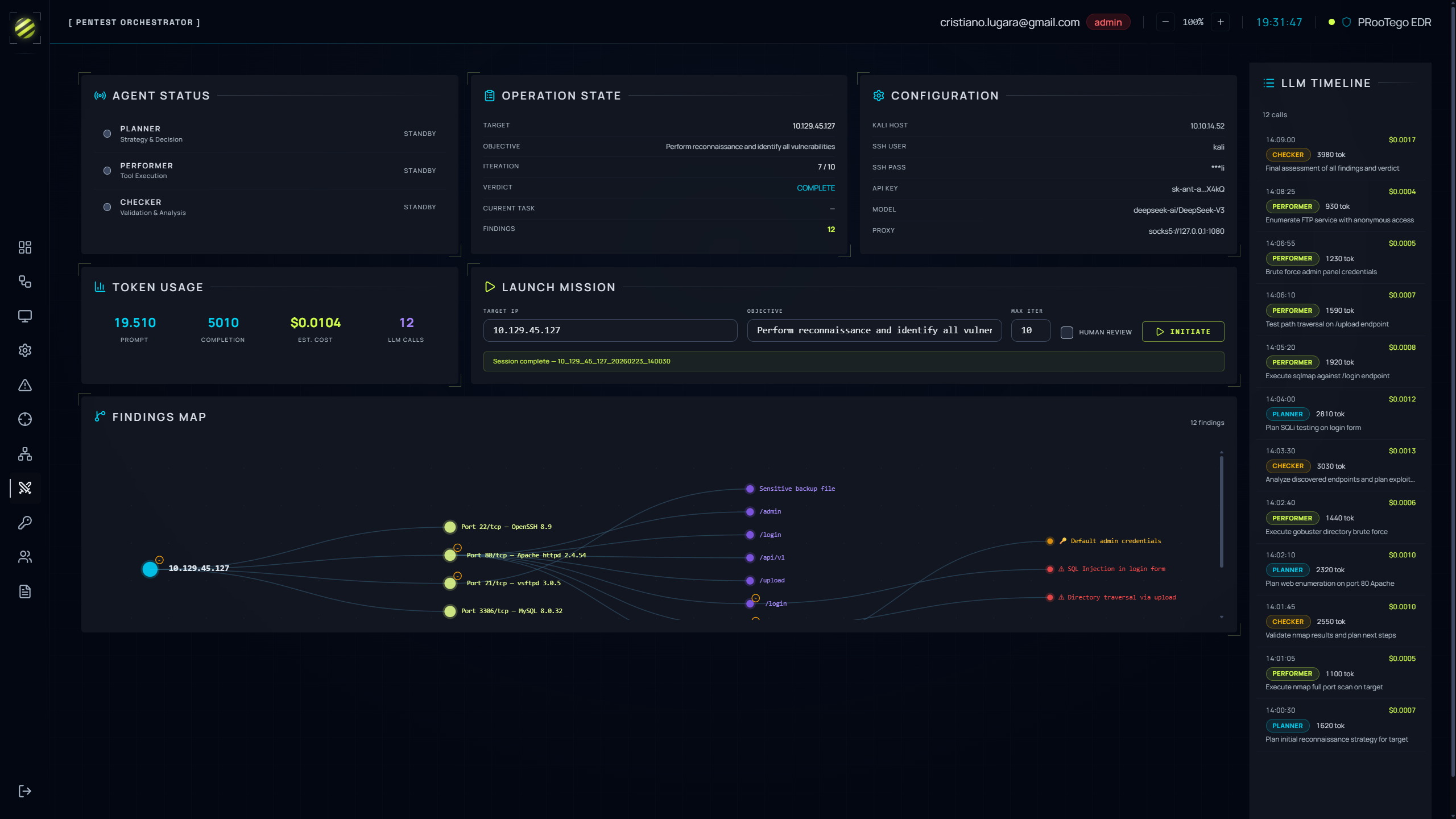
Integrated Pentesting Module
Built-in penetration testing to simulate attacks against your endpoints. Three-phase workflow — Planner, Performer, Checker — with a Human Review mode for production environments and a complete audit trail of every action.
- Planner, Performer, Checker workflow
- Human Review mode for production environments
- Interactive findings map with vulnerability details
- Full audit trail of every action and decision
Attack Chain Detection
Multi-phase attack sequences detected through correlated event chains. Each chain models a complete attack lifecycle — reconnaissance, access, escalation, exfiltration — alerting before the attack completes.
- Visual attack chain editor
- Multi-source event correlation
- Sigma rules with real-time distribution
- MITRE ATT&CK classification on every alert
Security by Design
End-to-end encryption on all communications. Full PKI with per-device cryptographic identities, automatic certificate rotation, and tamper-proof agent protection — agent cannot be stopped locally.
- mTLS with mutual certificate authentication
- Anti-tamper agent — cannot be stopped locally
- Encrypted data at rest
- Complete audit trail for NIS2/GDPR compliance
All communications secured with mTLS. Agent identity verified cryptographically on every connection.
One platform for every scenario
Defensive Posture Validation
Launch attack simulations against your infrastructure and verify in real time how defenses respond. Identify gaps before an attacker does, with a structured remediation workflow.
Advanced Attack Detection
Multi-source correlation of events from endpoints, network, firewalls, Active Directory, and email. Attack chains identify multi-phase sequences that individual tools miss.
Network Anomalies & Lateral Movement
The NIDS learns normal network behavior and immediately flags new devices, suspicious connections, unusual ports, and ARP spoofing attempts.
Insider Threat
Monitor access to sensitive files outside business hours, detect data exfiltration to external destinations, track privilege escalation with full audit trail.
Regulatory Compliance (NIS2, GDPR)
Immutable audit logs, automatic daily reports, MITRE ATT&CK matrix to demonstrate coverage, configurable data retention, and centralized role-based access management.
Enterprise AI Protection
Intelligent proxy with guardrails for every interaction with enterprise AI models. Detects and blocks prompt injection, data exfiltration and abuse in real time — protecting chatbots, copilots and AI agents from being manipulated or used as an attack vector.
Cyber Welfare
Companies can extend Prootego protection to employees' personal devices as a corporate welfare benefit. Protection runs on a completely separate environment from the main corporate one, ensuring employee privacy and full isolation from the company infrastructure.
Why choose Prootego
The problem: multiple vendors, no unified view
Today most companies manage security with 3, 4, or more different vendors: one for endpoints, one for the network, one for penetration tests, one for compliance. Each vendor sees only their piece. No one has the full picture. Data doesn’t talk, costs multiply, and gaps hide in the space between products.
One Vendor
Defense, network analysis, offensive security, and intelligence: all from one vendor. One contract, one support team, one platform to manage.
Data That Talks
When defense and offense live in the same platform, every piece of information enriches the others. No blind spots between products.
Controlled Costs
One integrated platform instead of multiple licenses, integrations to maintain, and vendors to coordinate. Less complexity, fewer hidden costs.
100% Italian
Development, support, and data entirely in Italy. Compliance with European regulations from day one, without depending on extra-EU infrastructure.
From Defense to Offense
Don’t just defend: test your defenses with real simulations and know exactly where to intervene. The improvement cycle is continuous and integrated.
Operational in a Day
No lengthy integration projects. Fast, automated setup: from decision to full protection in a single day.
Tailored Security Solutions
Whether you need full control over your security stack or prefer expert-managed operations, Prootego adapts to your needs.
EDR + XDR Platform
Complete endpoint protection with behavioral detection, network intrusion detection, SIEM log collection, and full MITRE ATT&CK coverage. Built on open standards — no vendor lock-in.
- Sigma Rules + Attack Chain Detection
- MITRE ATT&CK Full Coverage
- Built-in NIDS & SIEM Integration
- NIS2/GDPR-Ready Audit Logging
MDR Services
Everything in EDR/XDR, plus our expert analysts manage your security operations 24/7. Custom Sigma rules, dedicated support, and one-to-one client relationship.
- 24/7/365 SOC L1-L3 Monitoring
- Custom Sigma Rules & Dashboards
- Monthly Threat Reports + Pentest
- Dedicated Incident Response Team
Partner Dashboard (MSSP)
A dedicated operational portal for every Partner. Manage, monitor, and report on all end-client companies from a single point of control.
- Full visibility on managed companies
- Active device detail per company
- Real-time consumption monitoring
- Billing & accounting reports
- Separate instance per client — full isolation
Pay-as-you-protect
You only pay for the devices you protect, month by month. No annual contracts, no commitments, no minimum license requirements.
How it works
Your company uses its own devices and Prootego detects them automatically. Each month you are billed exclusively for the number of devices actually in use during that period.
If a device is no longer used, protection expires automatically after 30 days — the client stops paying for it, with no action required, no manual intervention, no hidden costs.
The only upfront cost is the dedicated infrastructure setup, covering installation, configuration, and platform deployment.
Use 50 endpoints, pay for 50. Next month you use 80, pay for 80. Use 10 fewer, the following month you pay for 70. Zero surprises, zero waste.
EDR/XDR/MDR
- Full EDR + XDR + NIDS Capabilities
- Sigma Rules & Attack Chain Detection
- MITRE ATT&CK Coverage Tracking
- NIS2/GDPR Compliance Audit Logging
- Integrated Pentesting Module (add-on)
Need a custom plan for large scale deployments?
Ready to secure your infrastructure?
Intelligent endpoint protection, total visibility, instant response. Trusted by security teams across Italy.
Stay Ahead of Threats
Subscribe to our newsletter for the latest insights on cybersecurity, threat intelligence, and product updates.
Subscribe on Substack